So, you’ve been asked to complete an SAQ for PCI DSS! Where do you start?
The first thing your business needs to understand is which payment channels it operates.
Why does this matter? There are different SAQs for different payment channels and it is important to choose the right one, not only to ensure that the risks that are relevant to that payment channel are mitigated but also to make sure that you are not putting in more effort than is required, wasting time and resources and possibly money too.
When deciding which SAQ applies to your business, you must ensure that the prerequisite criteria for each of the SAQs you are considering using can be met. You can find this information in the ‘Before You Begin’ section in each of the SAQs after the contents page.
The table below gives an indication to which SAQs are applicable to which payment channels:
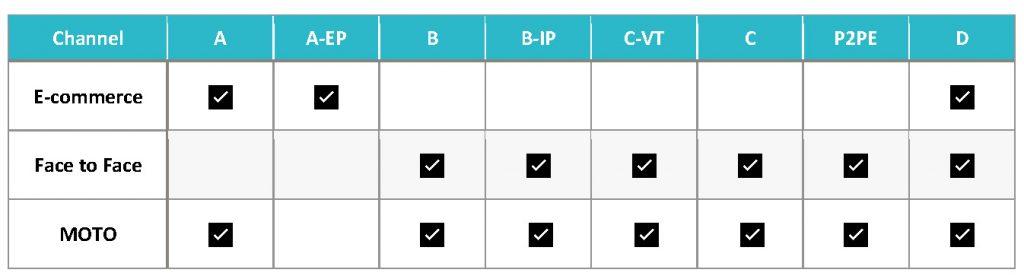
But what if you have more than one payment channel and you cannot use the same SAQ for all of them? You have 2 choices:
- Complete SAQ D which contains every requirement in the PCI DSS.
- Complete a separate SAQ for each of the payment channels.
Is one option better than the other? No, the choice is yours, or potentially your acquiring bank’s if they decide to mandate a particular one. However, if you opt to complete one SAQ for multiple payment channels, you must ensure that the applicable requirements are in place for each of the payment channels.
I have listed a couple of scenarios to allow for further explanation:
Scenario 1: You have an ecommerce channel and a MOTO channel which both fit into SAQ A.
Let’s look at Requirement 2.1a. Are vendor-supplied defaults always changed before installing a system on the network?
This applies to all default passwords in the ‘in scope’ systems in the ecommerce channel, like firewalls, routers, web servers, operating systems, and also to the ‘in-scope systems’ in the MOTO environment, so along with firewalls and routers, also the systems used by the call agents and any other systems that have been identified as being in scope. This is why it is really important to get the scope of the cardholder data environment correct at the very beginning.
Scenario 2: You have a MOTO channel which meets the SAQ B-IP prerequisites criteria and a Retail channel which meets the SAQ P2Pe prerequisite criteria. You decide to complete SAQ-D.
This is where it can get a little confusing as there will be some requirements that apply to one channel, some to the other, some to both and some to none.
It is recommended that the applicable requirements are identified before making a start on the assessment. Many clients have expressed frustration at trying to figure out what applies to their business as they are going through the questionnaire.
For this second scenario, it is a good idea to use SAQ B-IP and SAQ P2PE as a guide to allow you to identify which requirements apply so as not to assess unnecessary requirements. You can then mark the other requirements as being not applicable as the justification for doing so is that they are not included in the SAQs that the environment has met the prerequisite criteria for.
There are of course times when only SAQ-D will do as the channels don’t fit into any of the other SAQ models. However, sometimes there are simply tweaks that can be made so that they do meet the other SAQs. This is called scope reduction, and can be very cost effective, making savings on an annual basis when the PCI DSS anniversary date comes around again, whether that saving is a time based one or a financial based one.
Bridewell have provided many happy customers with scope reduction ideas and have also implemented scope reduction techniques in many sectors and for businesses of various sizes.



 Blogs
Blogs